Security was once the final checkpoint before a product shipped. In 2026, that model is no longer viable.
Modern software ships faster than ever. Hundreds of deployments happen each day across distributed cloud environments. Traditional security tools, built for monolithic applications and quarterly release cycles, simply cannot keep pace. The result is that vulnerabilities slip through, misconfigurations go unnoticed, and breaches become increasingly inevitable.
That is why the industry is rapidly embracing cloud-native DevSecOps as the new standard. It is a model that embeds security at every stage of the software delivery lifecycle. And in 2026, AI in DevSecOps has become the engine powering this transformation.
This blog explores how AI is reshaping security pipelines, what it means for your engineering team, and how you can get started practically and strategically.
Why Traditional DevSecOps Is No Longer Enough
Most security teams are still fighting modern threats with outdated tools. Rule-based scanners produce thousands of alerts, the vast majority of which are false positives. Manual code reviews cannot scale across hundreds of microservices. And by the time a vulnerability is caught in a legacy workflow, it is often already running in production.
The Core Gaps in Legacy Security Models
- Static rules cannot adapt: They flag known patterns but miss novel, contextual, or zero-day threats
- Alert fatigue is real: Security teams begin ignoring noise, and real threats hide inside it
- Silos between dev and security: Separate toolchains create friction, delays, and dangerous blind spots
- Cloud complexity outpaces manual processes: Multi-cloud, multi-region, and serverless environments demand a different approach entirely
Key Insight
Security can no longer be a gate at the end of a pipeline. It must be a continuous, intelligent layer woven into every stage from the first commit to production runtime.
What Is AI in DevSecOps? A Clear 2026 Definition
AI in DevSecOps means integrating machine learning models, predictive analytics, and intelligent automation into the security layers of a software delivery pipeline. It goes far beyond running automated scripts. AI learns your environment, adapts to new threats, and makes prioritization decisions that would take human analysts hours or days to complete manually.
Unlike traditional SAST or DAST tools that rely on static rule sets, AI-powered security platforms build dynamic models of what normal looks like in your specific environment and flag deviations in real time.
Core AI Capabilities in Modern Security Pipelines

AI-Powered Security Pipelines: How CI/CD Changes in 2026
The most visible impact of AI in DevSecOps is inside the CI/CD pipeline. AI does not just add another scanner. It transforms how every stage operates, from the moment a developer writes a line of code to the moment a workload runs in production.
The AI-Enhanced Pipeline Stage by Stage
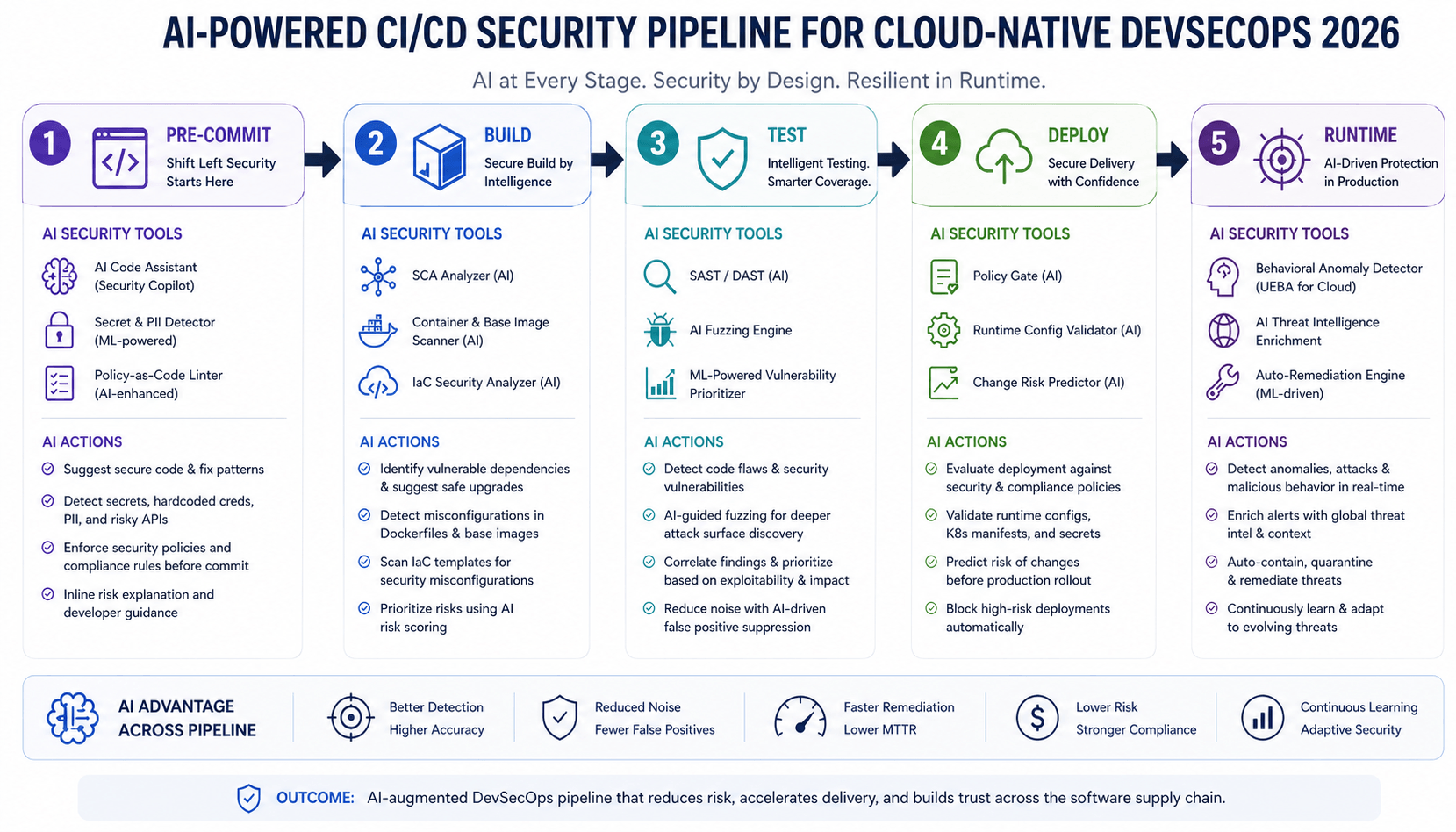
Pre-Commit: Catching Problems Before They Start
AI-powered IDE plugins scan code as developers type, flagging hardcoded secrets, insecure patterns, and vulnerable dependencies before a single line is pushed. This is shift-left security with AI in its most practical form. Problems that previously cost thousands of dollars to fix in production are resolved in seconds during development.
Build and Test: Smarter Scanning with Fewer False Positives
Traditional SAST tools flood developers with noise. AI-powered scanners understand context. They distinguish a test credential from a production secret, and they prioritize the vulnerabilities that actually matter to your specific stack. Automated security testing in DevOps using AI also generates adversarial test cases that human QA teams would rarely think to write.
Deploy and Runtime: Infrastructure as Code and Live Workload Protection
Infrastructure as code security is now an AI-first discipline. AI tools scan Terraform, Helm, and CloudFormation templates for misconfigurations with contextual intelligence that goes beyond pattern matching. At runtime, cloud workload protection platforms use ML-generated behavioral baselines to instantly detect anomalies across containers, pods, and serverless functions.
Kubernetes Security with AI: Protecting the Orchestration Layer
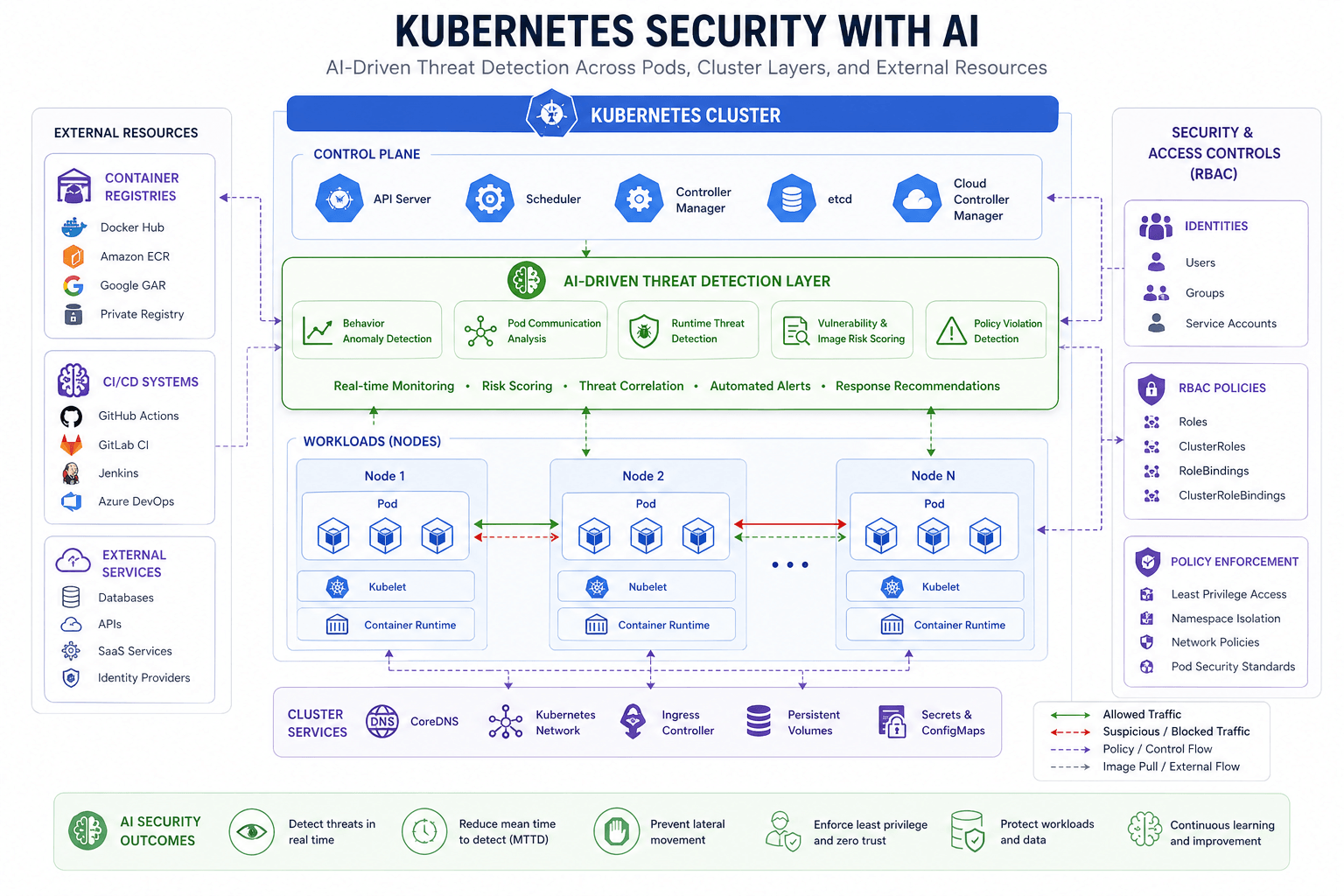
Kubernetes is the backbone of cloud-native applications and one of the most complex attack surfaces in modern infrastructure. Misconfigured RBAC policies, exposed API servers, and supply chain risks inside container images are among the most exploited vulnerabilities in cloud environments today.
How AI Strengthens Kubernetes Security
Kubernetes security with AI addresses problems that static tools fundamentally cannot solve at the speed and scale modern clusters demand:
- Runtime threat detection: ML models establish behavioral baselines per pod and alert when containers deviate, catching cryptomining, lateral movement, and privilege escalation in seconds
- Auto-generated network policies: AI observes real pod communication patterns and generates least-privilege network policies automatically
- Supply chain scanning: AI continuously audits container registries against CVE databases, flagging vulnerable base images before they are deployed
- Admission control: Policy engines powered by AI block non-compliant workloads from being scheduled, automatically and in real time
AI-Driven Threat Detection and Real-Time Security Monitoring
Traditional SIEMs process events retrospectively, alerting you after something has already gone wrong. AI-driven threat detection flips this model entirely by identifying threats before they cause damage.
From Reactive to Predictive Security
Modern real-time security monitoring in DevSecOps uses unsupervised learning to detect zero-day indicators of compromise before any signature exists. AI models trained on your environment recognize behavior that no human analyst would catch in time.
According to the NIST AI Risk Management Framework, organizations that adopt AI-based security monitoring reduce mean-time-to-detect by an average of 74 percent compared to traditional SIEM-only approaches.
What to Look for in an AI Security Monitoring Platform
- Cross-cluster log correlation with automatic triage and deduplication
- Natural language query interface so analysts can investigate without writing complex queries
- Automated incident response playbooks triggered by AI detections
- SBOM integration for real-time software supply chain visibility
- Unified multi-cloud dashboard with normalized alerting across AWS, GCP, and Azure
Infrastructure as Code Security: AI Stops Misconfigurations at the Source
IaC files including Terraform templates, Kubernetes manifests, and Ansible playbooks have become a primary attack vector in cloud-native environments. A single misconfigured storage bucket or overly permissive IAM role can expose an entire organization.
How AI Makes IaC Security Practical
- AI models trained on CVE databases and cloud provider security guidelines understand the context behind each configuration, not just its syntax
- They distinguish between an intentional override and an accidental misconfiguration, reducing false positives dramatically
- Auto-remediation features suggest or automatically apply policy fixes inline in the developer workflow
- This approach makes infrastructure as code security a natural part of development rather than a compliance burden
DevSecOps Best Practices 2026: A Practical Implementation Roadmap
Implementing cloud-native DevSecOps with AI does not require replacing your entire stack. The most successful teams start focused and expand deliberately.

Step-by-Step Adoption Framework
- Audit your current pipeline: Map every stage where security is absent, manual, or creating developer friction. These are your AI intervention points.
- Start with AI-powered SAST and secret scanning: Highest ROI, lowest disruption. Plug into your existing Git workflow without changing developer habits.
- Add cloud workload protection at runtime: Deploy behavioral monitoring across your container environment with ML-generated baselines.
- Expand to IaC scanning and Kubernetes policy enforcement: Prevent infrastructure misconfigurations from ever reaching production.
- Close the loop with real-time AI monitoring: Connect pipeline security signals to a unified monitoring layer for full-lifecycle visibility and automated response.
What to Look for in an AI-Powered DevSecOps Platform
The Future of DevSecOps with Artificial Intelligence
We are still in the early phases. The future of DevSecOps with artificial intelligence points toward capabilities that are already emerging in enterprise pilots and will become standard practice within the next 18 months.
What Is Coming Next
- Autonomous security agents: AI that detects threats and resolves them without human approval, within defined guardrails and policies
- LLM-assisted policy writing: Describe your security intent in plain English and AI generates the policy-as-code automatically
- Federated threat intelligence: Organizations share anonymized threat signals so AI models improve collectively without exposing sensitive telemetry
- Quantum-ready pipelines: AI-assisted migration to post-quantum cryptography standards embedded directly into cloud-native DevSecOps workflows
Organizations ready to lead this transformation can explore Pace Wisdom's Cloud Transformation Services and AI/ML Development Services, purpose-built to help enterprises embed intelligent security across their entire cloud-native delivery pipeline.
Conclusion: Security That Moves at the Speed of DevOps
The organizations winning in 2026 are not choosing between speed and security. They have made security a source of competitive advantage by making it intelligent, automated, and invisible to developers.
AI in DevSecOps is not a future aspiration. It is the operating standard today. Whether you are hardening CI/CD pipelines, protecting Kubernetes clusters, scanning infrastructure as code, or building real-time monitoring into your cloud workloads, AI is the force multiplier that makes all of it possible without slowing your teams down.
The question is not whether to adopt cloud-native DevSecOps with AI. The question is how fast you can get there and whether you have the right partner to guide the journey.
Frequently Asked Questions
What is cloud-native DevSecOps?
Cloud-native DevSecOps is the practice of integrating security controls, testing, and monitoring into every stage of a cloud-native software delivery pipeline, replacing the traditional security-at-the-end model with continuous, automated protection.
How does AI improve DevSecOps pipelines?
AI reduces false positives in vulnerability scanning, enables predictive threat detection, automates remediation, enforces infrastructure policies contextually, and provides real-time behavioral monitoring at the speed and scale that cloud-native environments require.
What is shift-left security with AI?
Shift-left security with AI means using intelligent scanning tools embedded in developer IDEs and early CI/CD stages to detect vulnerabilities before they reach production, where fixing them costs up to ten times more.
What are the top DevSecOps best practices in 2026?
- AI-powered SAST and secret scanning at the commit stage
- ML-based Kubernetes runtime protection and admission control
- Automated infrastructure as code scanning on every pull request
- Real-time threat monitoring with AI-driven triage and response
- Continuous AI-based vulnerability management across the full SDLC